2 min read
Apptainer 1.1.0 Is Here, with Improved Security and User Experience

Apptainer 1.1.0 Is Here, with Improved Security and User Experience
Here at CIQ, we’re excited to highlight an important announcement from the Apptainer community. Apptainer (formerly Singularity), a Linux Foundation project, announced version 1.1.0 of the most widely used container system for secure, high-performance computing (HPC). Apptainer is an open source project that executes HPC applications at bare-metal performance while being secure, portable, and 100% reproducible.
Apptainer 1.1.0 features improvements in security by reducing the attack surface for production deployments, as well as new features that make it easier to use. As was the case with Singularity, Apptainer features backwards compatibility, stability, added security, performance, and reproducibility.
Let’s take a peek at these new features:
Smaller Attack Surface
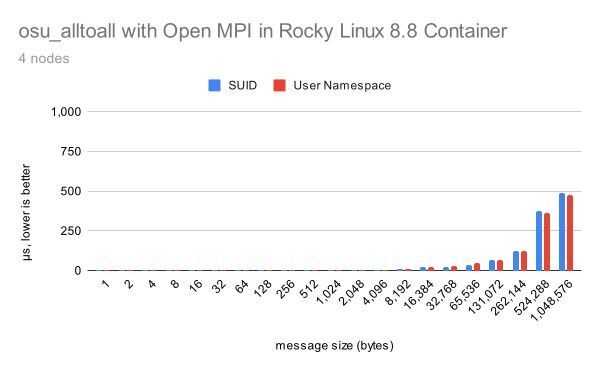
A fully rootless container runtime has been implemented in Apptainer 1.1.0, delivering a smaller attack surface. This is because Apptainer no longer installs a setuid-root portion by default. Instead, you can now execute common operations with only unprivileged user namespaces. If you install from binary packages (EPEL packages coming soon), the setuid portion can be restored by installing the apptainer-suid package. Or, if you install from source, it can be included by compiling with the mconfig –with-suid option. Here’s a deeper dive into Apptainer without setuid.
Specifically, improvements in this new feature include:
-
A squashfuse image driver that enables mounting SIF files without using setuid-root.
-
A fuse2fs image driver that enables mounting EXT3 files and EXT3 SIF overlay partitions without using setuid-root.
-
A persistent overlay option (–overlay) and –writable-tmpfs without using setuid-root. This requires unprivileged user namespaces and either a new enough kernel (>= 5.11) or the fuse-overlayfs command.
-
The ability to change SIF file mounts to use squashfuse_ll instead of squashfuse for improved performance. For even better parallel performance, a patched multithreaded version of squashfuse_ll is included in rpm and debian packaging.
Container Build Improvement
Another exciting enhancement in Apptainer 1.1.0 is that you have greater flexibility to set up containers without needing to use root. The new version extends the –fakeroot option to make it useful when /etc/subuid and /etc/subgid mappings have not been configured on the host. When this is the case, a root-mapped unprivileged user namespace (the equivalent of unshare -r) and/or the fakeroot command from the host will be tried. Together, these emulate the same mappings and are simpler to administer. You’ll find that this particular feature is especially useful with the –overlay and –writable-tmpfs options and for building containers unprivileged, because they allow installing packages that assume they’re running as root.
Ready to get started? Check out the complete release notes at the Apptainer GitHub repository:
https://github.com/apptainer/apptainer/releases
Watch our webinar, “Apptainer: Deep Dive, Use Cases, and Examples” to learn more about the key features that differentiate Apptainer from other runtimes.
Apptainer is a trademark of The Apptainer Series of LF Projects LLC. Find out more at https://lfprojects.org/policies.
Built for scale. Chosen by the world’s best.
2.75M+
Rocky Linux instances
Being used world wide
90%
Of fortune 100 companies
Use CIQ supported technologies
250k
Avg. monthly downloads
Rocky Linux